The stonefish is named for its ability to camouflage itself among ocean floor debris. It is highly venomous, and its sting can be fatal to any human unfortunate enough to step on one. Recognizing and avoiding the stonefish is a swimmer’s best defense, but that is easier said than done.
Like the stonefish, the email phish (or simply “phish”) is a master of disguise, lurking in inboxes and waiting for users to step on them. Its venom is kept in links and attachments, and one click delivers a sting of malware to the user’s computer system.
Sometimes the phish is in a text message, also referred to as a SMiShing attack, and is disguised to look like an official company text message.
Recognition and avoidance are a user’s best defense against these phish, but that, too, is easier said than done.
Fish/phish analogy aside, Trevor Buxton, a fraud awareness and communications manager and Certified Fraud Examiner with PNC Bank offers safety tips for individuals and small businesses to help recognize and avoid phishing attacks.
Know the Red Flags
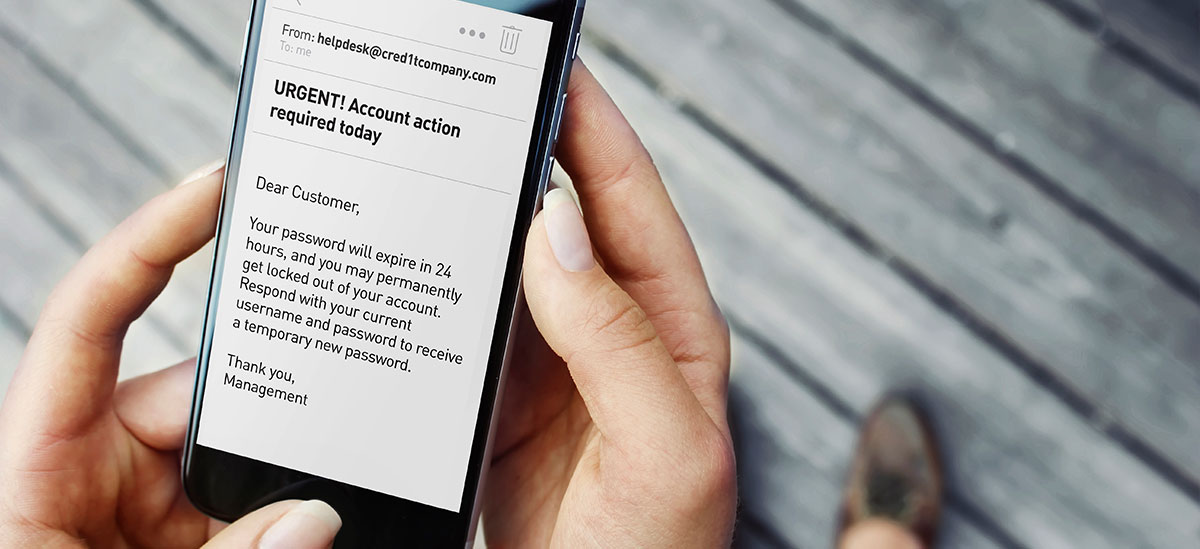
Phishing attacks are designed to resemble legitimate correspondence and rely on a user’s inability to spot them in order to succeed. Email or text messages containing certain red flags should alert users to a possible phishing or SMiShing attack:
- Misspellings
- Grammatical errors
- Offering fantastic prizes
- Creating a sense of urgency
- Requesting personally identifiable information (PII)
- Requesting User IDs and Passwords
- Threatening with consequences
- Making demands
- Take Action
Email address spoofing is also a common tactic of phish. The user may not notice an email address has been changed from “@homelender.com” to “@home1ender.com” and may recklessly click links and open attachments, which introduce malware.
Small Businesses & Phish
Small businesses have the added threat of phishing or SMiShing attacks designed to mimic vendors, couriers, suppliers, clients, colleagues, etc. Employees should ensure that email and text messages coming from these third parties is legitimate.
Such business relationships also can serve as backdoor attack routes for phish to infiltrate the objective business itself. Example: The Target data breach of 2013 started with a phishing attack against one of its third-party refrigeration contractors.
Understanding third-party cybersecurity policies and procedures will help small businesses decide which ones are taking it seriously.
Business Email Compromise (“BEC”) is another threat affecting businesses of all sizes. Thieves use BEC to dupe employees into transferring money, releasing HR and payroll data, or exposing trade secrets and intellectual property.
BEC can be carried out by spoofing an employee’s email address, or by gaining control of an employee’s legitimate email account. BEC attacks often appear to come from C-level managers or other positions of authority within the business, adding a level of prestige to the unauthorized request.
Phight Back
Fortunately, there are things which can help individuals and small businesses detect and avoid a phish:
- Hover the cursor over the sender’s email address, which should bring up a “mouseover” box containing the sender’s actual email address. Inspect it for signs of spoofing.
- Use email’s “forward” feature rather than “reply.” “Forward” forces the user to type in a known and trusted email address, whereas “reply” will respond directly to the phisher.
- In a suspected phish, do not click links or respond to a text message requesting personal or financial information like credit card numbers, Social Security numbers or other banking information. It is best practice to contact the company directly by typing in a known URL address directly into your Internet browser and not use information contained in the suspect email/text.
- Do not open attachments in a suspected phish.
- Do not call phone numbers contained in a suspected phish. Go directly to a known source of information for contact information, such as the company’s legitimate website.
- Regarding BEC, call the requestor to confirm any unusual demands for money transfers, HR or employee payroll data, or trade secrets or intellectual property.
- If practical, refrain from posting personnel organizational structures in the public domain. Phishers can use this information to make their BEC scams more effective.
- Keep employee leave and absence information off of social media accounts. Phishers can use this knowledge to craft “emergency situation” BEC scams.
Upon spotting a phish, delete it. Do not click any links or open any attachments. Do not forward it to friends and colleagues.
If compelled to forward a phish, forward it to the FBI’s Internet Crime Complaint Center (IC3).
For more helpful tips on cybersecurity, visit the Federal Trade Commission website